In CrushFTP version 10 we can integrate our One Time Password (OTP) based authentication feature with Google's and Microsoft's software-based token device Google Authenticator and Microsoft Authenticator, using Time based OTP (TOTP). The user can register a QR code into Google Authenticator or Microsoft Authenticator app.
Server side configuration
#
You will need to enable one of our OTP methods, using SMS or Mail based OTP, and enable the Validated logins checkbox. The user needs to be able to log in at least once, without OTP, or with the other OTP settings.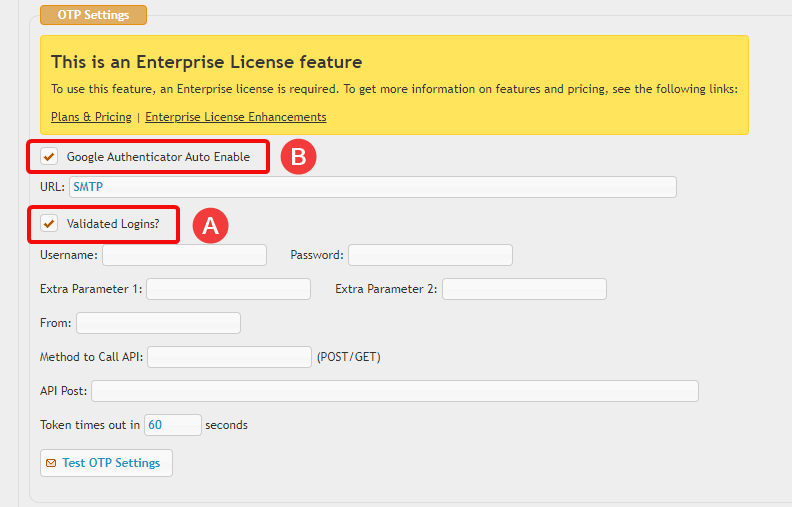
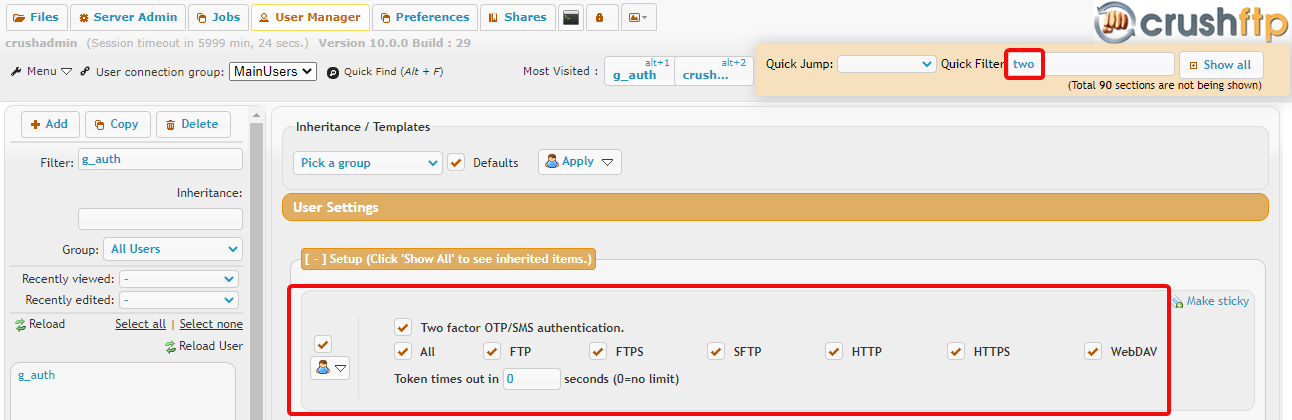
The second step is to configure the user account with Two Factor Authentication
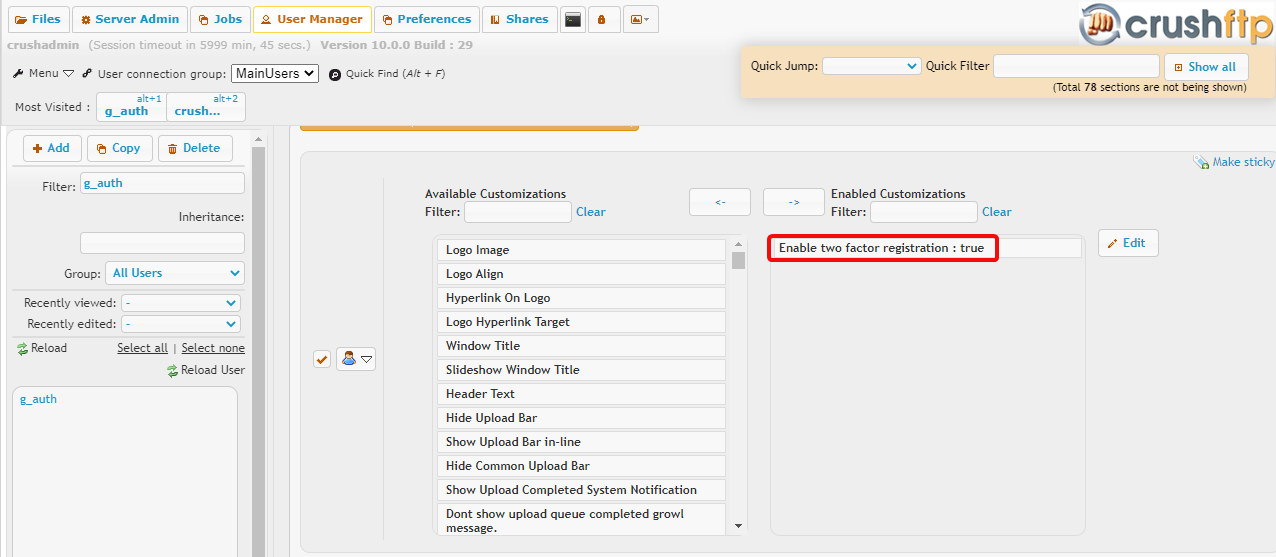
and enable the two factor QR code generator which will appear in the user's User Options menu when they are logged in.
Client / token device configuration
#
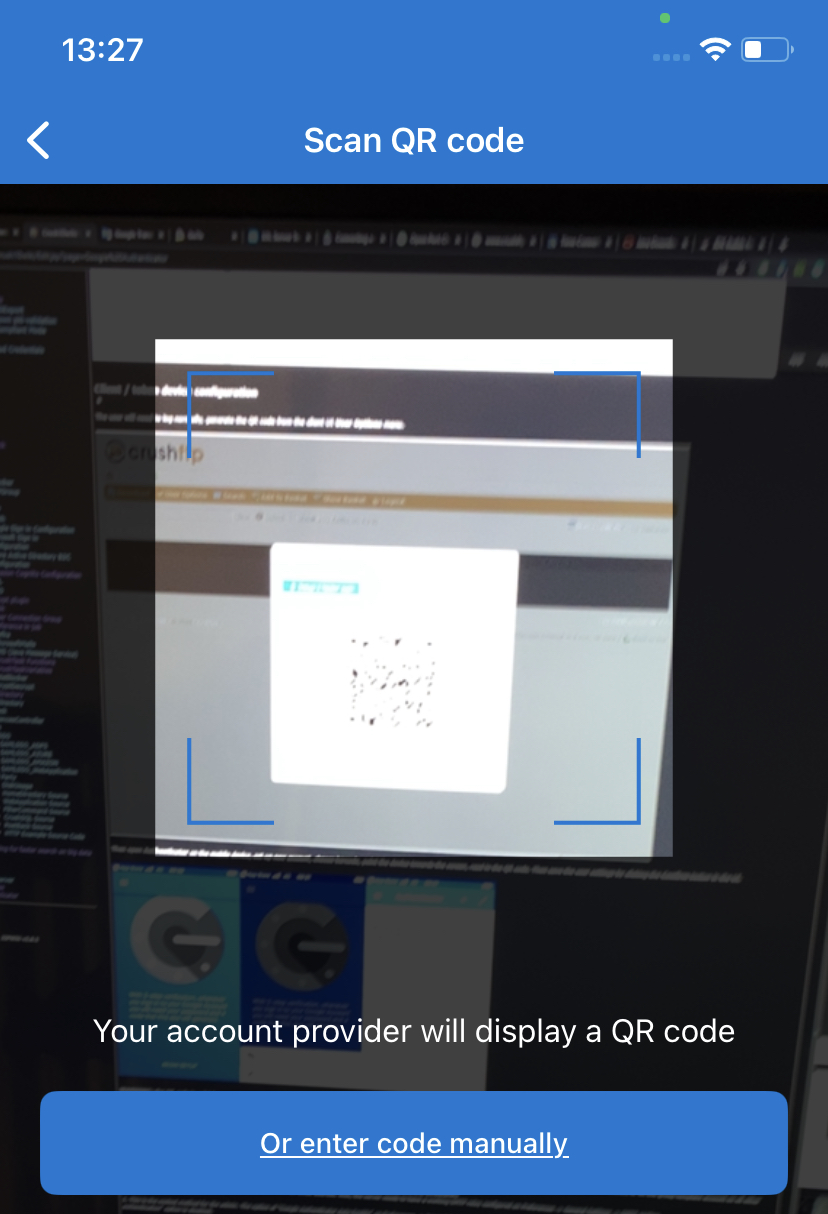
The user will need to log in normally, generate the QR code from the client UI User Options menu.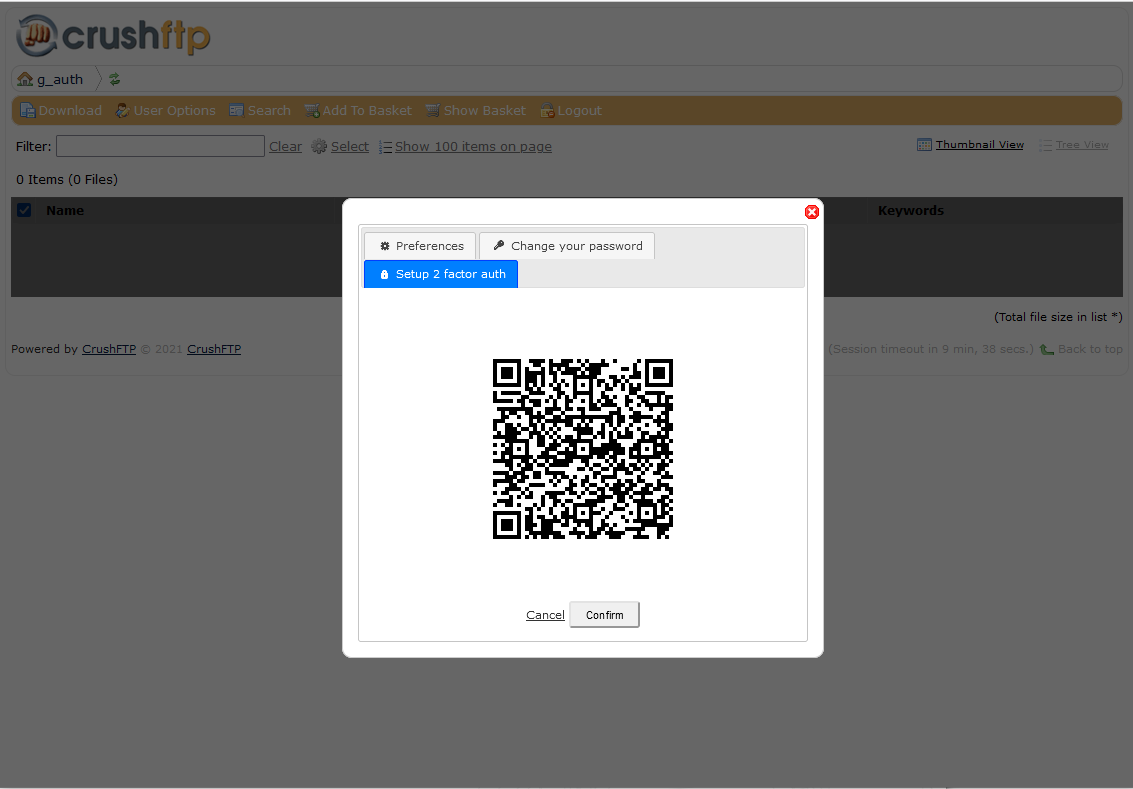
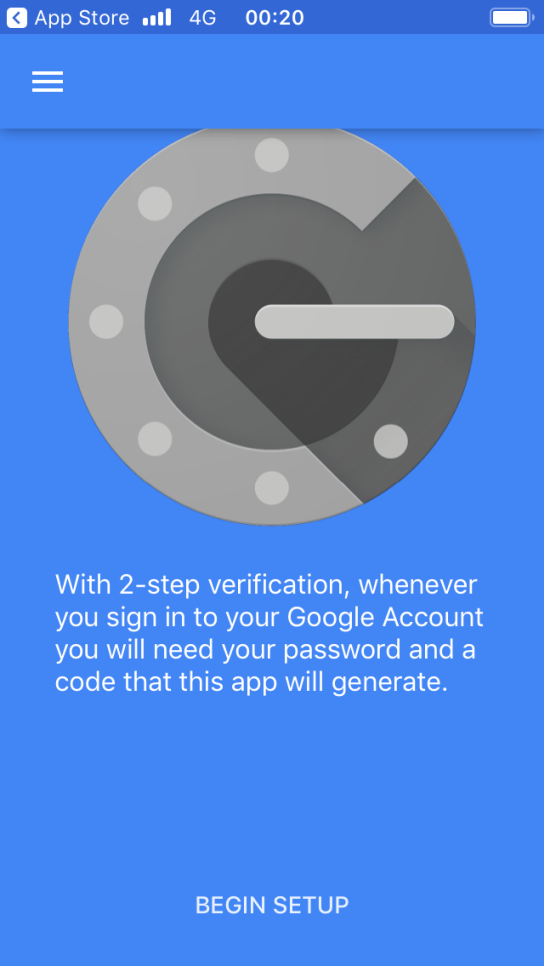
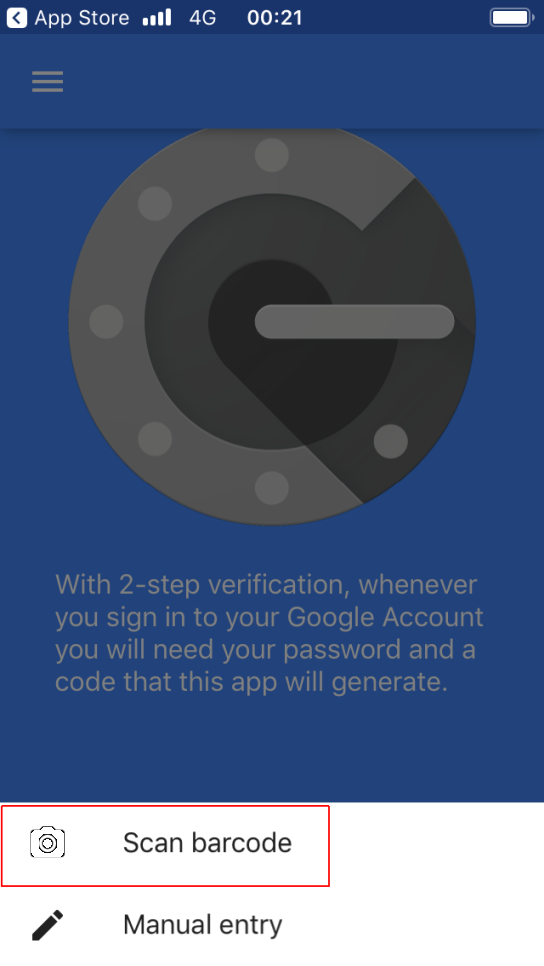
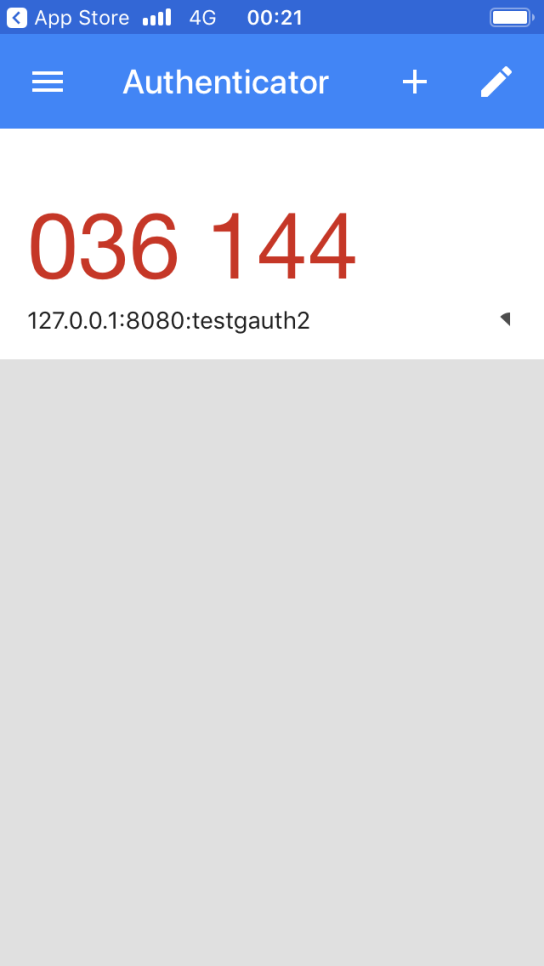
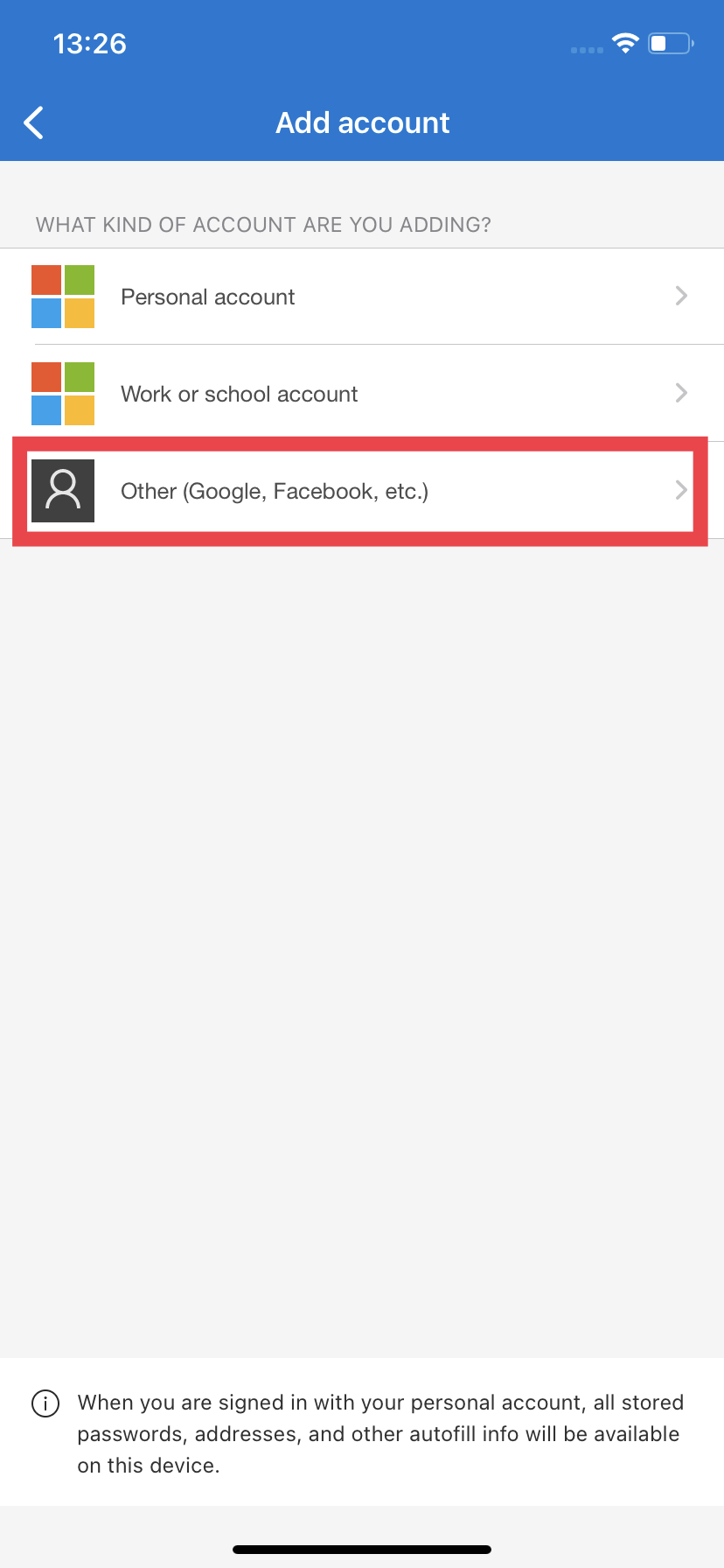
Then open Authenticator on the mobile device, set up a new account, choose to scan barcode, point the device towards the screen, and read in the QR code. Then save the user settings by clicking the Confirm button in the UI.
Google Authenticator
 |
 |
 |
Microsoft Authenticator
 |
 |
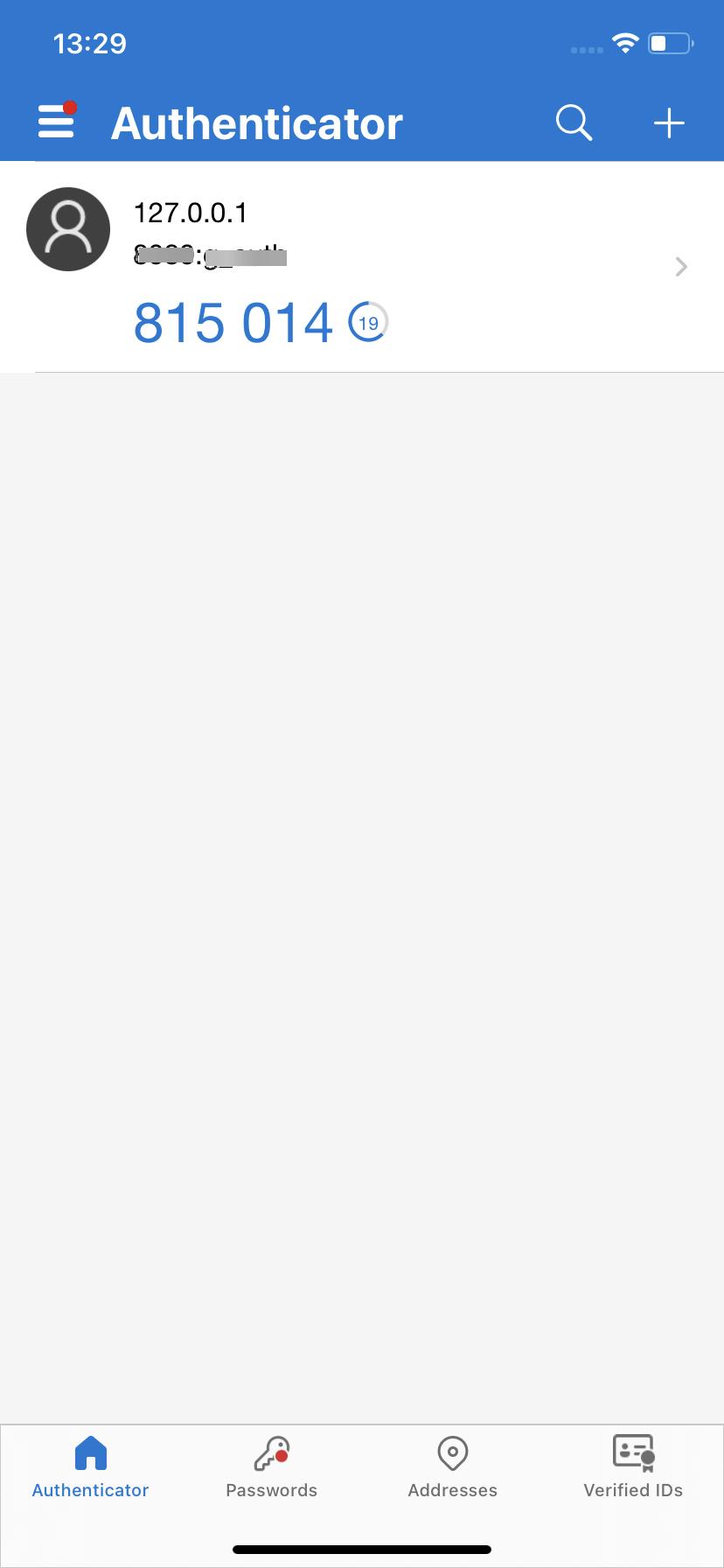 |
WARNING: the QR code is valid for one minute, if the time window is missed you will need to generate new, or it will not save. Once a secret key has been saved from the QR code, and confirmed, it can only be reset by a server administrator. It's a one-time process.
Possible scenarios regarding the cooperation of admin and the end-user:#
Prerequisites:
-a working Google Authenticator app on a mobile device
-in the User Manager -> user -> Webinterface -> Available customizations section the "Enable two factor registration" is set to True. This can be enabled on the "default" template account or on the group template account so all other users will inherit the setting from the template user.
-on Preferences -> General Settings -> OTP section the "Validated Logins" option must be enabled (A on the first screenshot)
-for the 2nd option the user account has to be configured with an email address. Also, the server needs to have a working SMTP relay configured on Preferences -> General Settings -> SMTP section.
1. This is the easiest method for the admin. The option of "Google Authenticator Auto Enable" on Preferences -> General Settings -> OTP section is enabled (B on the first screenshot). In User Manager the "Two factor OTP/SMS authentication" option is disabled.
The end-user logs in with username and password, and initializes the "Setup of 2 factor auth" via the User Options button, scans the QR code, and hits the Confirm button. In the background, CrushFTP writes the Two factor authentication Secret to the user account and takes care of enabling the "Two factor OTP/SMS authentication" option for the user.
2. The option of "Google Authenticator Auto Enable" on Preferences -> General Settings -> OTP section is left in disabled state. In User Manager the "Two factor OTP/SMS authentication" option is enabled by the admin.
The end-user enters its username and password on the login page. A popup will be prompted asking for the email-based token, then the user is allowed to log in and initialize the Setup of 2 factor auth via the User Options button. Next time won't get an email, and at the token popup enters the 6-digit code generated by Google Authenticator.
3. The option of "Google Authenticator Auto Enable" on Preferences -> General Settings -> OTP section is left in disabled state. In User Manager the user doesn't have the "Two factor OTP/SMS authentication" option enabled
The end-user logs in with username and password, and initializes the Setup of 2 factor auth via the User Options button, scans the QR code, and hits the Confirm button. In the background, CrushFTP writes the Two-factor authentication Secret to the user account, but the Admin needs to activate the "Two factor OTP/SMS authentication" option for the user.
DMZ - Main node scenario: on Preferences -> General Settings -> OTP section the "Validated Logins" option must be enabled on the DMZ node, so the DMZ gives the two-factor authentication to the Main node.
Add new attachment
List of attachments
| Kind | Attachment Name | Size | Version | Date Modified | Author | Change note |
|---|---|---|---|---|---|---|
jpg |
Clipboard05.jpg | 139.3 kB | 1 | 05-Dec-2023 05:32 | Ada Csaba | |
png |
Clipboard05.png | 116.6 kB | 1 | 05-Dec-2023 05:32 | Ada Csaba | |
jpg |
IMG_2500.jpg | 191.7 kB | 1 | 05-Dec-2023 05:32 | Sandor | |
jpg |
IMG_2501.jpg | 464.9 kB | 1 | 05-Dec-2023 05:32 | Sandor | |
jpg |
IMG_2502.jpg | 52.0 kB | 1 | 05-Dec-2023 05:32 | Sandor | |
png |
enable_two_factor.png | 42.5 kB | 2 | 26-Feb-2024 03:15 | Ben Spink | |
png |
qr_otp.png | 1,990.7 kB | 1 | 26-Feb-2024 03:00 | Ben Spink | |
png |
servercfg001.png | 23.0 kB | 5 | 05-Dec-2023 05:32 | Sandor | |
png |
servercfg002.png | 54.1 kB | 4 | 05-Dec-2023 05:32 | Sandor | actualized v10 |
png |
servercfg002.png.png | 54.1 kB | 1 | 05-Dec-2023 05:32 | Sandor | actualized v10 |
png |
servercfg003.png | 64.4 kB | 4 | 05-Dec-2023 05:32 | Sandor | |
png |
servercfg004.png | 43.2 kB | 4 | 05-Dec-2023 05:32 | Sandor | |
png |
tokencfg001.png | 101.9 kB | 2 | 05-Dec-2023 05:32 | Ada Csaba | |
png |
tokencfg002.png | 96.2 kB | 2 | 05-Dec-2023 05:32 | Ada Csaba | |
png |
tokencfg003.png | 37.4 kB | 2 | 05-Dec-2023 05:32 | Ada Csaba |
