S3 integration
Allows you to use a S3 bucket as the backend filesystem. However, since S3 isn't hierarchical, you only get simulated folders, and no ability to rename, and some other gotchas about how S3 works. These aren't limitations we impose, but just due to the design decisions S3 made in that it's intended for static item consumption and not as a location for holding and manipulating file names.
1. Configuration.
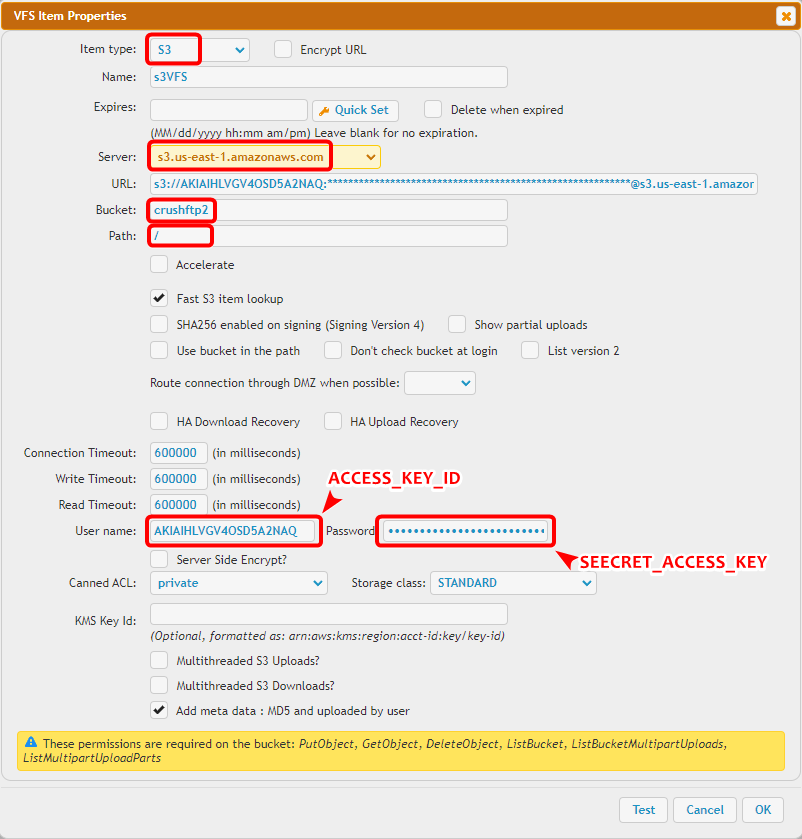
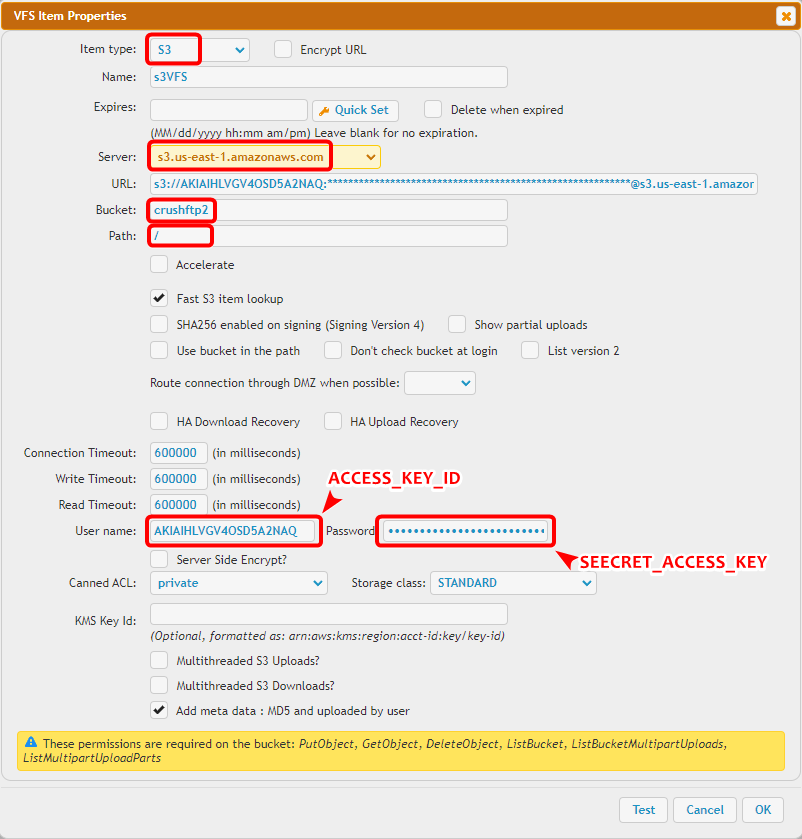
The URL should look like this (Replace the URL with your corresponding data!):
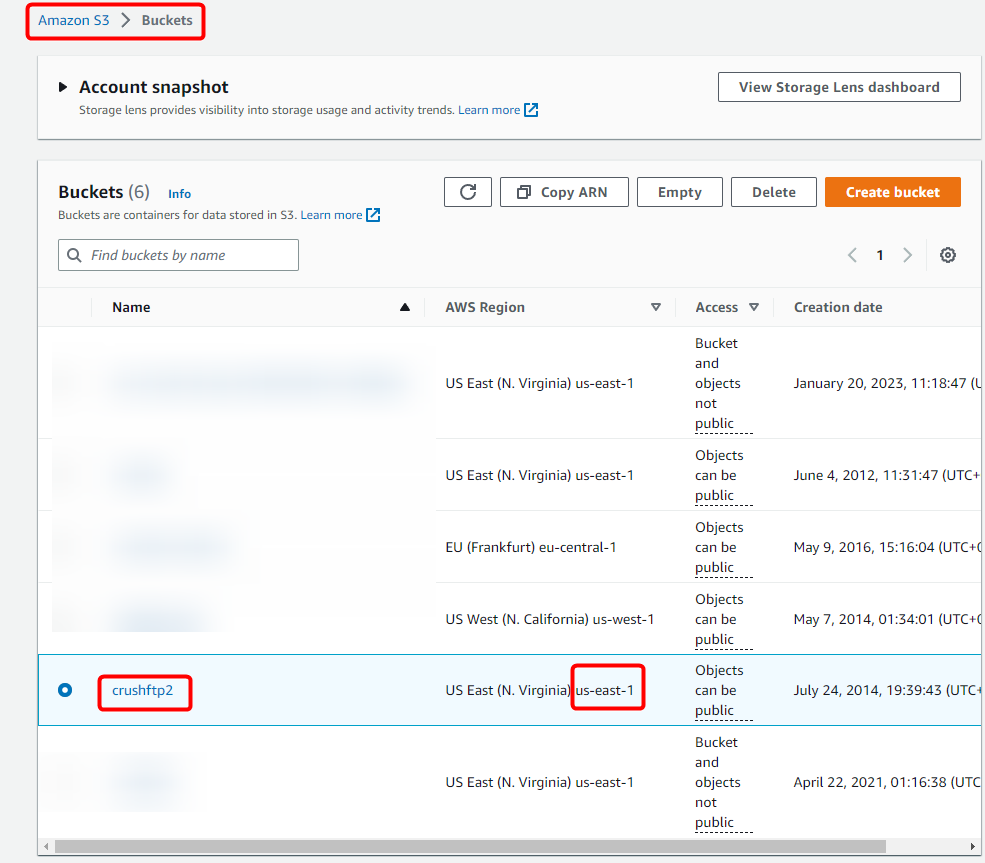
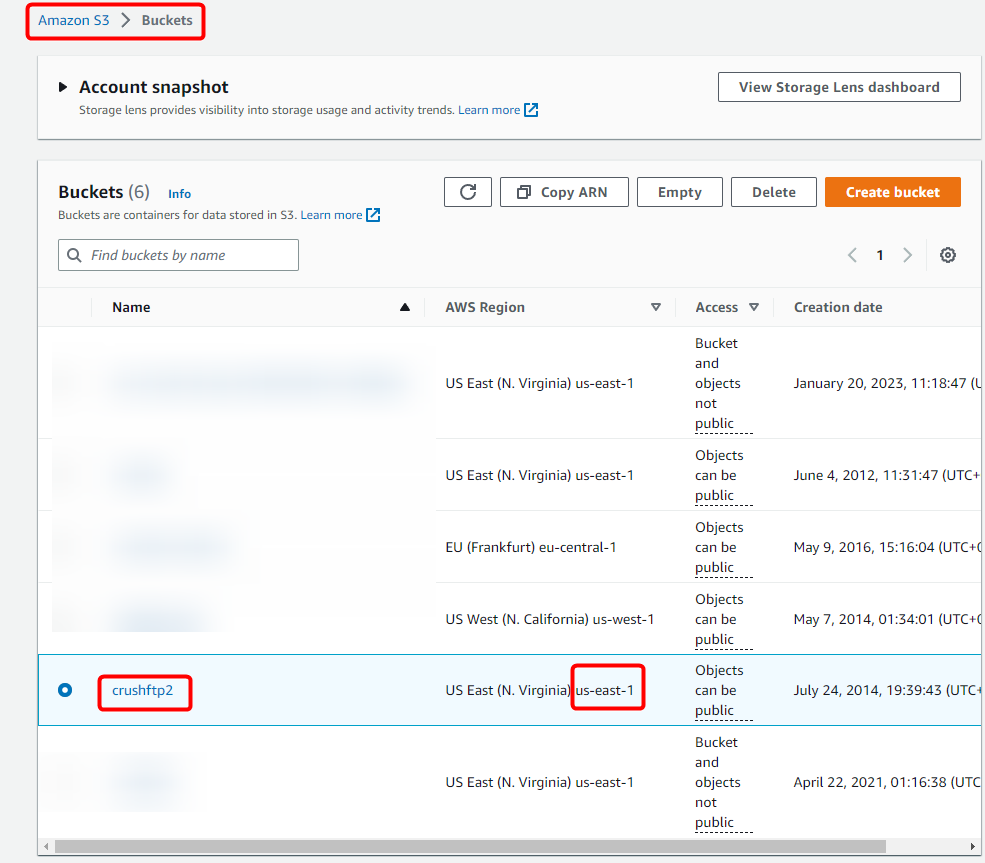
The security credentials (Access key ID and Secret Access Key) were offered to save at S3 user creation. The server and bucket information can be found on the S3 portal (at AWS site S3 -> Buckets).
Then paste them on the appropriate fields in CrushFTP.
We support the IAM auth scenario too, its just not the default mode. Setting the S3 username to "iam_lookup" and S3 password to "lookup" will use this method.
The following policy permissions are needed on S3:
2. Access other cloud storage through S3 REST API
Google Cloud - Google Cloud Storage Integration
BackBlaze(b2) - BackBlaze(b2) integration
3. Assume Role access
You can use IAM roles to delegate access to your AWS resources. With IAM roles, you can establish trust relationships between your trusting account and other AWS trusted accounts. (for more info see: https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_create_for-user.html , and https://docs.aws.amazon.com/STS/latest/APIReference/API_AssumeRole.html
, and https://docs.aws.amazon.com/STS/latest/APIReference/API_AssumeRole.html )
)
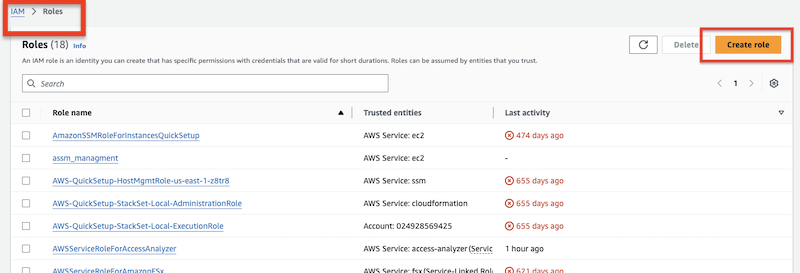
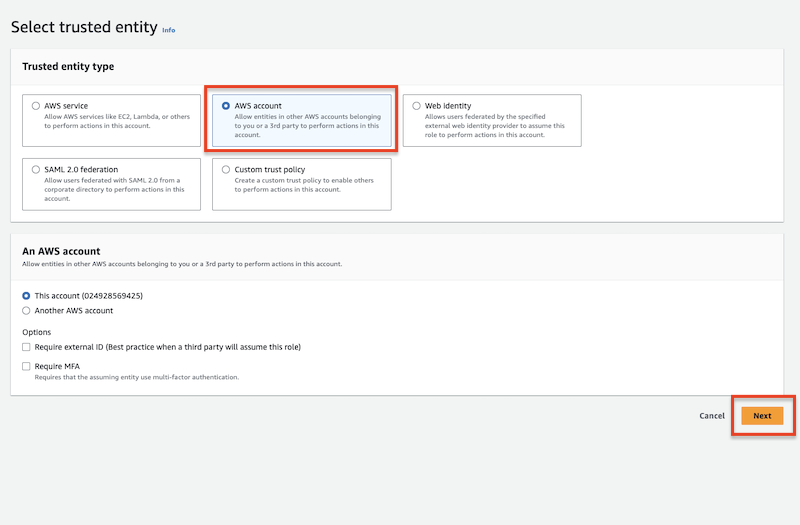
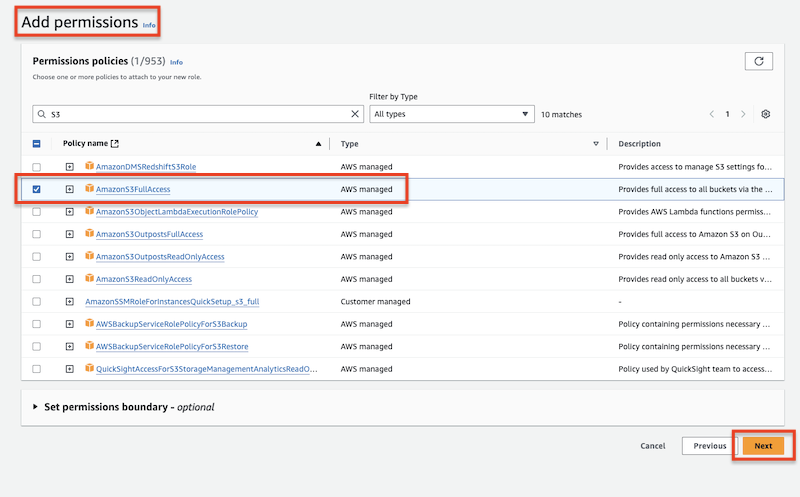
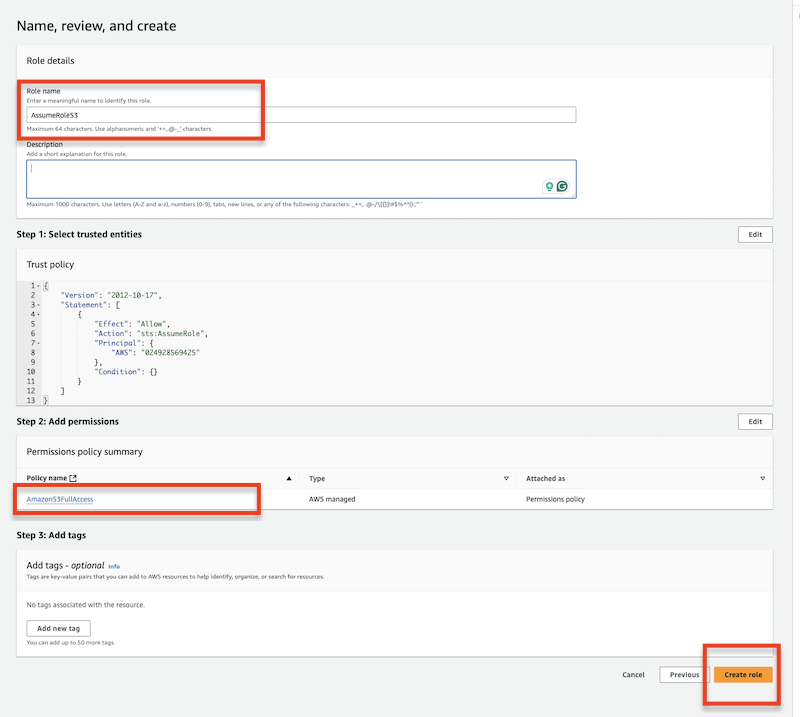
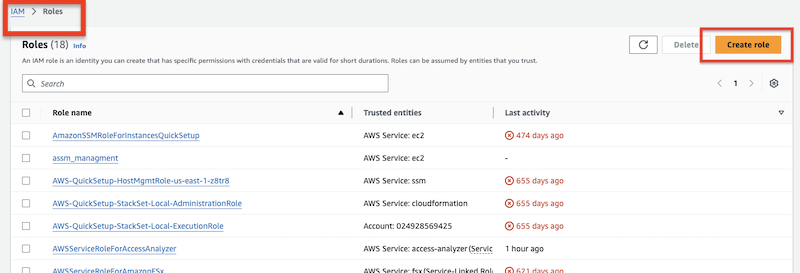
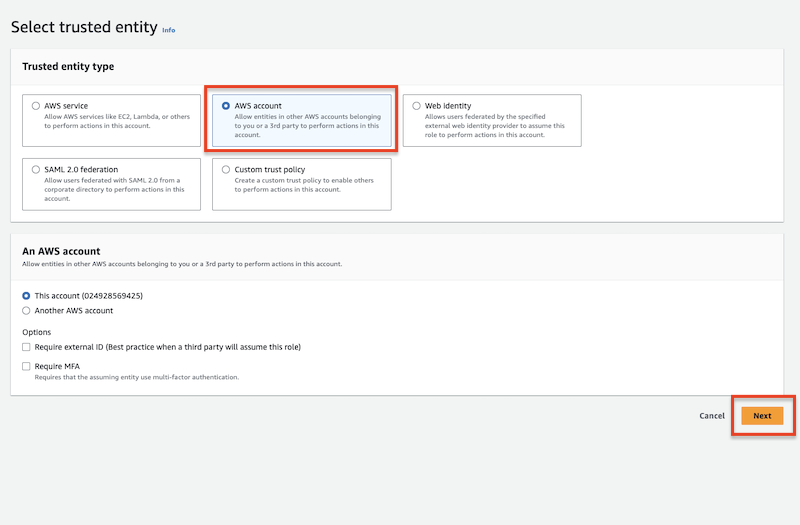
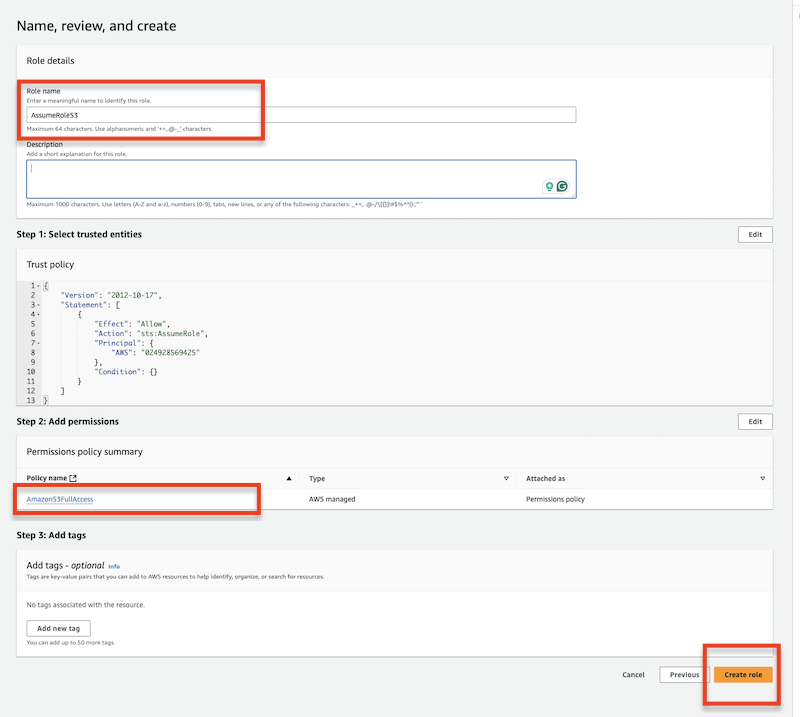
Create the assume role at Identity and Access Management (IAM):
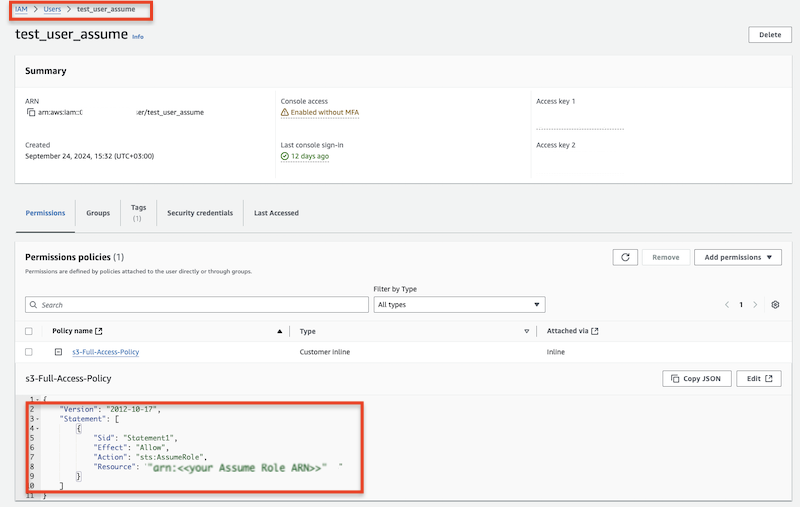
Add permission policy to the specified user. This policy will use the above-created assume role.
Use the specified user's Access key and Secret along with the Assume Role ARN to obtain s3 access.
Allows you to use a S3 bucket as the backend filesystem. However, since S3 isn't hierarchical, you only get simulated folders, and no ability to rename, and some other gotchas about how S3 works. These aren't limitations we impose, but just due to the design decisions S3 made in that it's intended for static item consumption and not as a location for holding and manipulating file names.
1. Configuration.
#
The URL should look like this (Replace the URL with your corresponding data!):
s3://ACCESS_KEY_ID:SEECRET_ACCESS_KEY@SERVER/BUCKET/
The security credentials (Access key ID and Secret Access Key) were offered to save at S3 user creation. The server and bucket information can be found on the S3 portal (at AWS site S3 -> Buckets).
Then paste them on the appropriate fields in CrushFTP.
We support the IAM auth scenario too, its just not the default mode. Setting the S3 username to "iam_lookup" and S3 password to "lookup" will use this method.
The following policy permissions are needed on S3:
"s3:GetBucketLocation", "s3:ListAllMyBuckets", "s3:ListBucket", "s3:ListBucketMultipartUploads", "s3:PutObject", "s3:AbortMultipartUpload", "s3:ListMultipartUploadParts", "s3:DeleteObject", "s3:GetObject", "s3:GetObjectAttributes"
2. Access other cloud storage through S3 REST API
#
Google Cloud - Google Cloud Storage Integration
BackBlaze(b2) - BackBlaze(b2) integration
3. Assume Role access
#
You can use IAM roles to delegate access to your AWS resources. With IAM roles, you can establish trust relationships between your trusting account and other AWS trusted accounts. (for more info see: https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_create_for-user.html
 , and https://docs.aws.amazon.com/STS/latest/APIReference/API_AssumeRole.html
, and https://docs.aws.amazon.com/STS/latest/APIReference/API_AssumeRole.html )
)Create the assume role at Identity and Access Management (IAM):
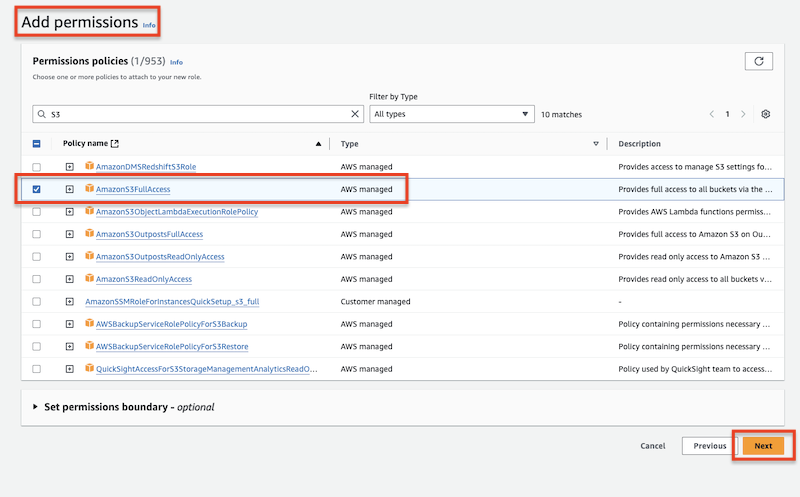
Add permission policy to the specified user. This policy will use the above-created assume role.
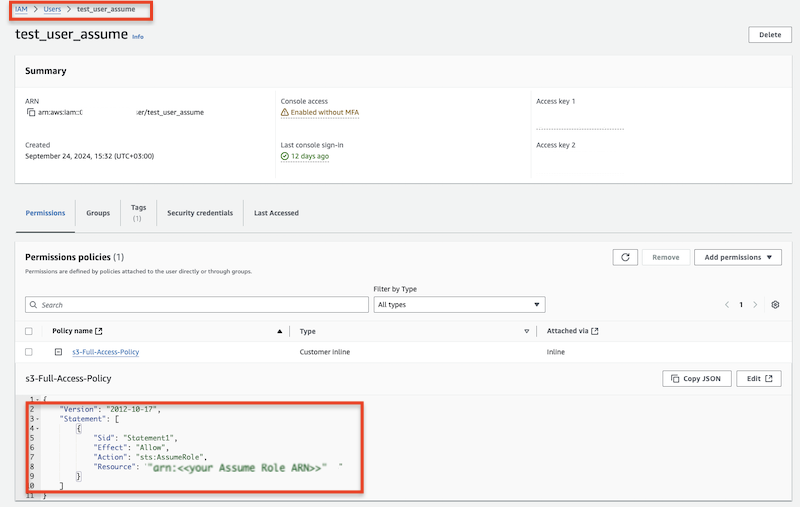
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "Statement1",
"Effect": "Allow",
"Action": "sts:AssumeRole",
"Resource": "arn:aws:iam::XXXXX:role/AssumeRoleS3"
}
]
}
Use the specified user's Access key and Secret along with the Assume Role ARN to obtain s3 access.
Add new attachment
Only authorized users are allowed to upload new attachments.
List of attachments
| Kind | Attachment Name | Size | Version | Date Modified | Author | Change note |
|---|---|---|---|---|---|---|
png |
S3_VFS_config.png | 54.2 kB | 1 | 05-Dec-2023 05:32 | Sandor | |
png |
S3_bucket_info.png | 99.3 kB | 1 | 05-Dec-2023 05:32 | Sandor | |
png |
assume_create_role_final_check... | 119.7 kB | 1 | 07-Oct-2024 07:25 | krivacsz | |
png |
assume_role_entity_type.png | 94.2 kB | 1 | 07-Oct-2024 07:16 | krivacsz | |
png |
assume_role_s3_access.png | 140.2 kB | 1 | 07-Oct-2024 07:20 | krivacsz | |
png |
assume_role_user_permission_po... | 103.9 kB | 1 | 07-Oct-2024 07:36 | krivacsz | |
png |
assume_role_vfs_settings.png | 183.7 kB | 2 | 07-Oct-2024 08:02 | krivacsz | |
png |
create_assume_role.png | 84.5 kB | 1 | 07-Oct-2024 07:14 | krivacsz |
«
This particular version was published on 07-Oct-2024 07:57 by krivacsz.
G’day (anonymous guest)
Log in
JSPWiki